Someone Tried to Hack Etherscan [Using the Comment Section]

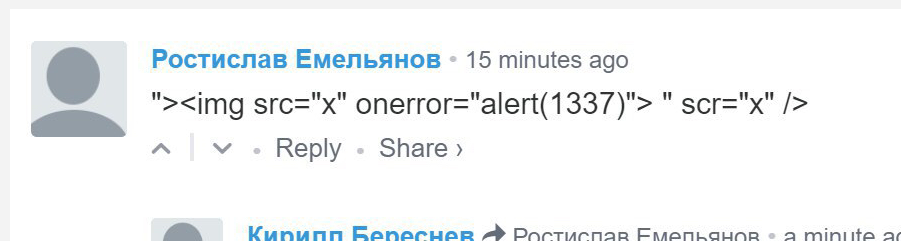
Ethereum block explorer Etherscan has thwarted an apparent hacking attempt in which the would-be attacker attempted to use the comment section to serve up malicious code.
Users attempting to access the official Etherscan website on Monday were met by a suspicious Javascript popup message reading “1337,” suggesting that an attacker was attempting to inject malicious code into the website, likely in an attempt to execute an ethereum phishing scam.
Upon investigating the matter, Etherscan determined that the attack had originated in the website’s comment section, which allows users to comment on ethereum addresses and is powered by third-party comment hosting service Disqus.
The website promptly disabled the summarized Disqus comments at the site page footer and, according to an announcement posted on Reddit , is now working on a patch that will encapsulate the footer HTML and prevent another similar incident from occurring in the future.
According to MyCrypto developer Michael Hahn, it does not appear that the website had served up any malicious code by the time developers had noticed the attack.
“XSS, in this case a javascript injection, was taking advantage of Disqus comments that people use to comment on addresses. It doesn’t appear that Etherscan had been serving malicious code when it was noticed. Disqus comments on Etherscan.io were disabled until a security patch is published which will encapsulate/encode the field to remove the vulnerability to XSS.”
However, it’s likely that the hacker had something far more sinister in mind than creating annoying pop-up messages. For instance, the attacker could have ultimately hoped to inject code designed to trick users into exposing their private keys or sending a transaction to a hacker-controlled wallet.
Thankfully, this particular scheme does not seem to have had led to any loss of funds, though other recent incidents have not been resolved quite so cleanly.
Earlier this month, hackers infiltrated Hola, a free virtual private network (VPN) extension for Google Chrome, and used that access to monitor the activity Hola users who accessed ethereum web wallet service MyEtherWallet.
In February, hackers phished approximately $1 million from users attempting to contribute to the Bee Token initial coin offering (ICO) by impersonating the token sale’s operators on social media and in email conversations.
Featured Image from Shutterstock