
The hackers behind last week’s $530 million Coincheck heist have once again begun moving the stolen XEM tokens, marking the beginning of what will likely be a cat-and-mouse game to launder the funds.
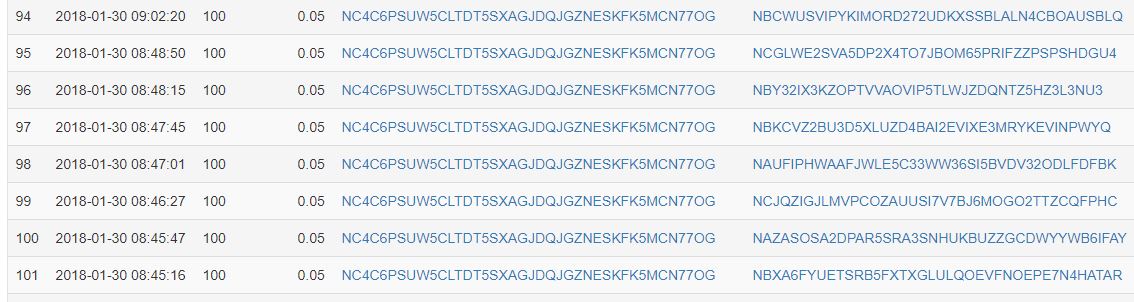
Blockchain data demonstrates that the hackers made a litany of transfers from their primary address to a variety of other addresses on Jan. 30. Each transaction transferred 100 XEM, worth approximately $77 at the present exchange rate.
That represents a small percentage of the 500 million XEM the hackers raked in during the theft, but it likely indicates that they are attempting to launder the stolen funds.
“When people look to launder these types of funds, they sometimes spread it into smaller transactions because it’s less likely to trigger (exchanges’) anti-money laundering (mechanisms),” Tom Robinson, co-founder of Elliptic, a cryptocurrency security firm in London, told Reuters.
Indeed, while the hackers are sitting on a fortune that is now spread across a variety of addresses, it does them little good unless they can launder the funds into a form that cannot be connected to them.
Attempting to launder too many tokens at one time will not only place too much downward pressure on the NEM price but could also trigger red flags at cryptocurrency exchanges, who would then most likely freeze the funds and turn them over to authorities.
The NEM Foundation, which has been tracking the funds in an attempt to prevent them from being spent or laundered, confirmed that the hackers had attempted to transfer them to cryptocurrency exchanges.
“[The hackers are] trying to spend them on multiple exchanges. We are contacting those exchanges,” the NEM Foundation Vice President Jeff McDonald said. “I would assume that they are going to get away with some of the money,” he added.
The hackers could be using these small transfers to test whether trading platforms will immediately freeze funds sent from an address known to be associated with the theft.
If successful, they could then send a larger sum from another address and convert it into a privacy-centric cryptocurrency, such as Monero, which would allow them to shield the latter stages of the laundering process.
Their end goal is most likely to convert the funds into Bitcoin, which is by far the most fungible cryptocurrency and can be traded for a wide variety of fiat currencies.
Many of the hackers’ attempts to launder the funds will probably be thwarted, particularly following an incident that is believed to be the largest cryptocurrency exchange theft in history. However, even limited success will net them a small fortune.
Featured image from Shutterstock.
