McAfee’s Unhackable Bitfi Wallet Hacked Again, Security Researchers Await Bounty
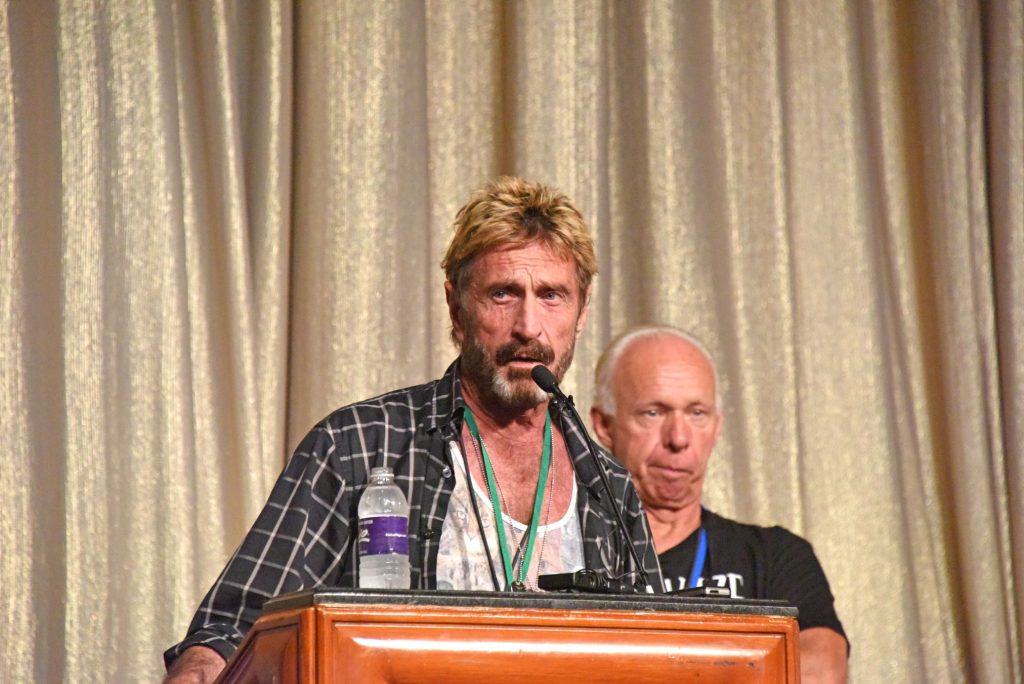
On the home page of hardware wallet Bitfi’s website, it is hard to miss these words attributed to the company’s chairman, John McAfee: “The world’s first un-hackable storage for cryptocurrency & digital assets.”
But for the umpteenth time, the security of the hardware wallet has been severely compromised. In the most recent incident according to Hard Fork, security researchers at Pen Test Partners were able to send signed transactions using Bitfi thereby fulfilling a vital requirement for the hardware wallet’s bounty program.
“Well, that’s a transaction made with a MitMed Bitfi, with the phrase and seed being sent to a remote machine,” Andrew Tierney, a security consultant at Pen Test Partners, wrote on Twitter. “That sounds a lot like Bounty 2 to me.”
Three Conditions
Compared to Bitfi’s initial bounty which was offering a prize of US$250,000 the second bounty was relatively meager at only US$10,000. To claim the second bounty the rules include among others modifying the hardware wallet’s firmware and then connecting to the Bitfi dashboard. The final condition to be met involves ensuring that the secret phrase of the user or their private keys are transmitted to a third party while ensuring that the Bitfi dashboard continues functioning normally.
Per Tierney, the team was able to significantly modify the firmware and consequently intercept communications between the hardware device and the wallet. And to prove that the device was still connected to the dashboard and working perfectly the researchers displayed messages on the screen.
Team Effort
According to Tierney, hacking the hardware wallet involved teamwork with various individuals and entities making varying contributions.
As CCN.com recently reported, the device was rooted (gaining administrator or privileged access) at the beginning of this month by an information security expert who subsequently found a suite of apps that included GPS and Wi-Fi trackers. This was viewed as a serious security issue since the tracking apps were discovered to be connecting to various web services include the Chinese online search giant Baidu.
Less than ten days later 15-year old Saleem Rashid, a hacking prodigy, was able to install Doom gaming application on the device and play it. This raised concerns that by having weak or non-existent tamper protections, malicious actors could easily install malware leaving it vulnerable to manipulation. Additionally, there were concerns that with root access the device could be easily reprogrammed.
Bitfi’s response to the whole saga resulted in a series of missteps and bad publicity. As a result, the firm recently won the Pwnie Award for the Lamest Vendor Response during the BlackHat USA conference that was held in Las Vegas, Nevada.
Featured image from Flickr/NullSession .
