 Government will never have to mine on hardware it buys. At least, they’ll leave the buying up to you.
Government will never have to mine on hardware it buys. At least, they’ll leave the buying up to you.
This week a court in Virginia indicted Kim Dotcom and six of his alleged coworkers. The event is part of an ongoing attempt to prosecute Kim Dotcom. Since 2012, Virginia attorneys have accused Dotcom of Copyright Infringement, Racketeering, Money Laundering, and Wire Fraud among other charges.
Those filings led to the January, 2012 raid on Dotcom’s home in New Zealand. Seventy-six police and two helicopters assisted by the FBI seized Dotcom, $17 million in luxury cars, televisions and works of art. His bank accounts in New Zealand and around the world were frozen, denying access to $175 million dollars.
Kim waited in prison until the end of February. Released on bail, his incentive to flee diminished – fugitive status forfeits assets to the state.
Also Read: How to Launder Stolen Bitcoins
Asset Forfeiture is a nationwide policing initiative in America. It exists to
“remove the tools of crime from criminal organizations, deprive wrongdoers of the proceeds of crimes, recover property that may be used to compensate victims, and deter crime.”
It gives a government officials the ability to take your property until you can prove it came from a lawful origin.
It works because the government never charges you, the person. The government accuses the property. I.e. United States v. $10,000 or United States v. One Parcel Known as 352 Northup St., 40 F., instead of United States v. Kim Dotcom. Property can’t defend itself, so it automatically loses, and the government takes possession.
In 2007, the Department of Justice published a Strategic Plan to guide law enforcement and enhance the capability, reach and effectiveness of the program. In it, the government reminds us:
When assets are taken away, crime is fought.
Cash seized by law enforcement is added to their budget. Vehicles and equipment may be re-purposed by the organization and deployed at their discretion. The cherry on top, the US has formed international partnerships to seize accounts around the world.

Instead of seizing cars, electronics, and dollars they seized a Dotcom-sized mining operation and turned it over to the World’s Most Benevolent Spy Organization? Exchange operator Charlie Shrem was given jail time because transactions linked to Silk Road passed through his business. What if, instead, transactions linked to Silk Road passed through his mining operation? Every user who downloads the block chain possesses the same data. What if it’s one of them?
That’s the Asset Forfeiture Bitcoin attack – seize your enemies property and use it against them.
“If the Department is to continue to be effective, it must think strategically. The stakes are high. The national security and lives of Americans are at risk. The government cannot and will not fail in this important endeavor.”- United States Department of Justice Asset Forfeiture Program, Strategic Plan
Since the burden is on you proving your assets are lawful it makes it almost impossible to recover cash from the police. In Philadelphia, over 8,000 forfeiture cases were filed by the city against African American and Hispanic residents. The average take amounted to $550. In Washington D.C., victims of asset forfeitures may be charged up to $2,500 to challenge a police seizure in court.
The regulation creates an environment where we no longer have a justice system. Police do not protect and serve. It is a system of “Eat what you Kill” and the main course is the cash in your wallet.
The moral of the story, if you plan to break the law, make sure you use cheap stuff. The ‘punishment’ for forfeiture is arbitrary. A vehicle seized for a drunk driving infraction does not consider whether the car is worth $700 or $70,000.
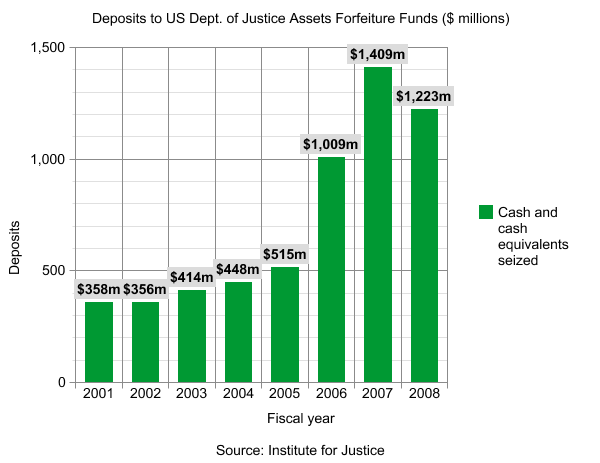
Since 2005 the dollar value of forfeitures nearly tripled. Up from 2005’s $515 million, 2007 nearly tripled the dollar amount at $1.4 billion. It’s almost like there was some Strategic Plan released to do just that.
“The foregoing history illustrates that, contrary to the misconception held by some, civil forfeiture is not a novel process, but is rather a powerful tool with deep roots in America’s law enforcement tradition.” – United States Department of Justice Asset Forfeiture Program, Strategic Plan
The origin of asset forfeiture in the United States starts with British Maritime law in the 1600s. Any trader importing or exporting from the colonies was required to abide by British law. For example, if a Spanish trader’s ship did not fly the British flag while conducting business it was breaking the law.
It wasn’t practical to send agents to Spain to apprehend the trader, extradite and prosecute them. The British solution was easier than chasing foreigners around the globe – seize the property.
This week the US seized Kim Dotcom’s assets. Kim is considered a fugitive. Would Bitcoin have been able to protect his fortune? Why are Ross Ulbricht‘s alleged bitcoins up for auction?
In connection with Edward Snowden, email service Lavabit was ordered by a judge to surrender encryption keys. Rather than betray their customers, Lavabit shut down.
If Kim’s wealth had been stored with Bitcoin could a judge have ordered him to turn over the keys? Probably. It’s also possible, in the realm of theory crafting, Kim could (or perhaps does) have a brain wallet where no physical connection between Kim and his coins would exist.
However, what is for certain, if Kim had been operating Bitcoin miners they would sit alongside his luxury cars and electronics. If a part of the government so desired, they could be appropriated and used to whatever ends they desire.
Enforcement prefers to target endpoints. The same approach applies with Bitcoin. If cryptocurrency is a big enough threat that it becomes illegal, then asset forfeiture will be the strategy that inflicts the greatest harm. It will start with the largest mining operations, businesses, and voices and work its way down. There will never be an arms race in mining equipment between the network and a government. By virtue of asset forfeiture, the miners could just be seized. That much control could centralize mining, destroying faith in the algorithm and integrity of the block chain.
Sure, we would change coins/algorithms, and that would force decentralization back to CPU/GPU and FPGA, perhaps underground ASIC production. It quickly becomes a cyberpunk fantasy where malware botnets and rogue system administrators reign.
Images from Shutterstock & Wikimedia.
