Bithumb Hacked Again: $13 Million in EOS, 20 Million XRP On the Move

Bithumb, one of South Korea's largest crypto exchanges, has been hacked again. | Source: Shutterstock
Bithumb was hacked for the second time in less than a year as attackers managed to steal 3 million EOS coins and 20 million XRP. The subsequent laundering of the $21 million dollar haul was then tracked in real time by a twitter analyst, as the hacker swapped the tainted coins for other cryptocurrencies on non-KYC exchanges.
Bithumb hacked again: 3 million EOS gone!
The news broke late on Saturday morning (UST) as crypto entrepreneur and analyst Dovey Wan relayed reports apparently coming from a security firm who were auditing for Bithumb.
The attack was at first feared to have struck the cryptocurrency’s exchange’s cold wallet. However it was later confirmed that it was an online ‘hot wallet ’ that had been hacked. As Wan stated, this is the second time in less than a year that Bithumb has fallen prey to the same trap:
“And this is the second time Bithumb saw a MAJOR hack, last time it’s hacked with a loss over $30m.. lol and after the first hack it was STILL able to get the fiat license from Korea and WTF??”
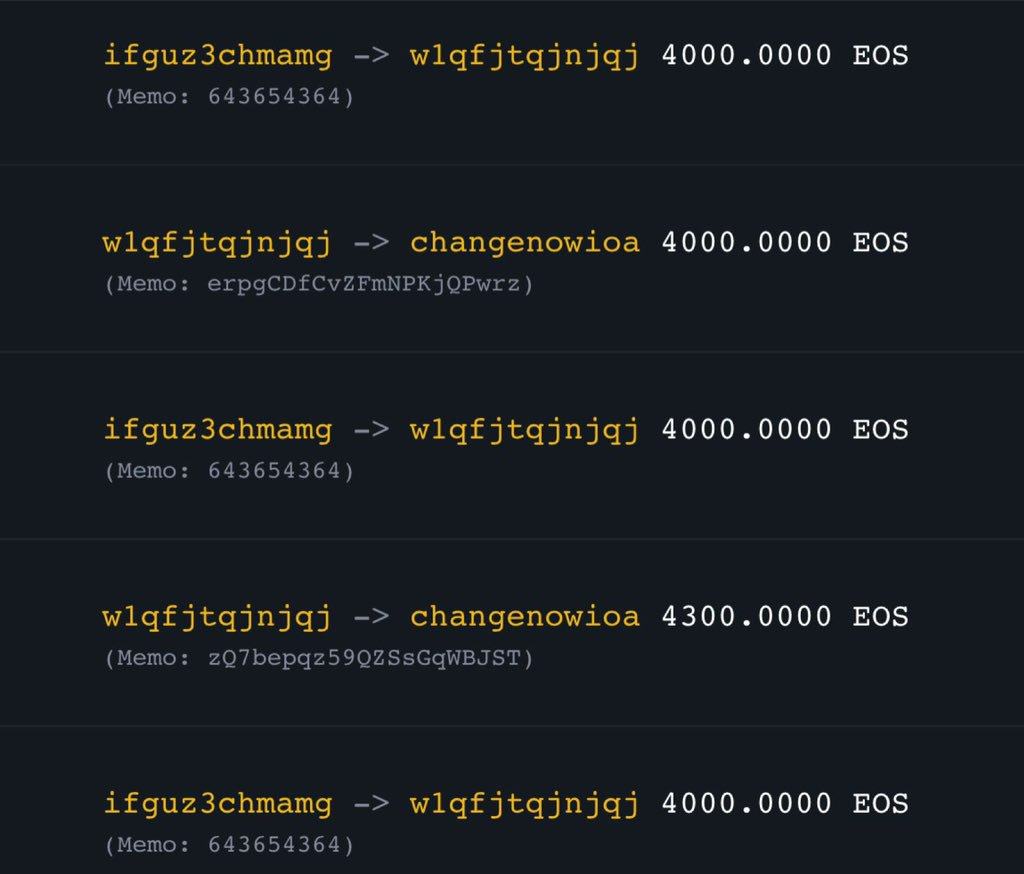
As more news filtered through it was revealed that the EOS was on the move via the non-custodial, non-KYC exchange ChangeNow. Dovey Wan posted this screenshot of substantial sums of EOS passing through ChangeNow’s transaction logs.
It gets worse: 20 million XRP hacked
It was then revealed that XRP had also been stolen in the attack, with 20 million coins leaving the hot wallet along with the EOS. The stolen XRP funds equated to around $6 million. Wan tweeted the XRP address on the hot wallet that had been hit:
“XRP hacked wallet address – rLaHMvsPnPbiNQSjAgY8Tf8953jxQo4vnu stolen 20,000,000 xrp (worth $6,000,00)”
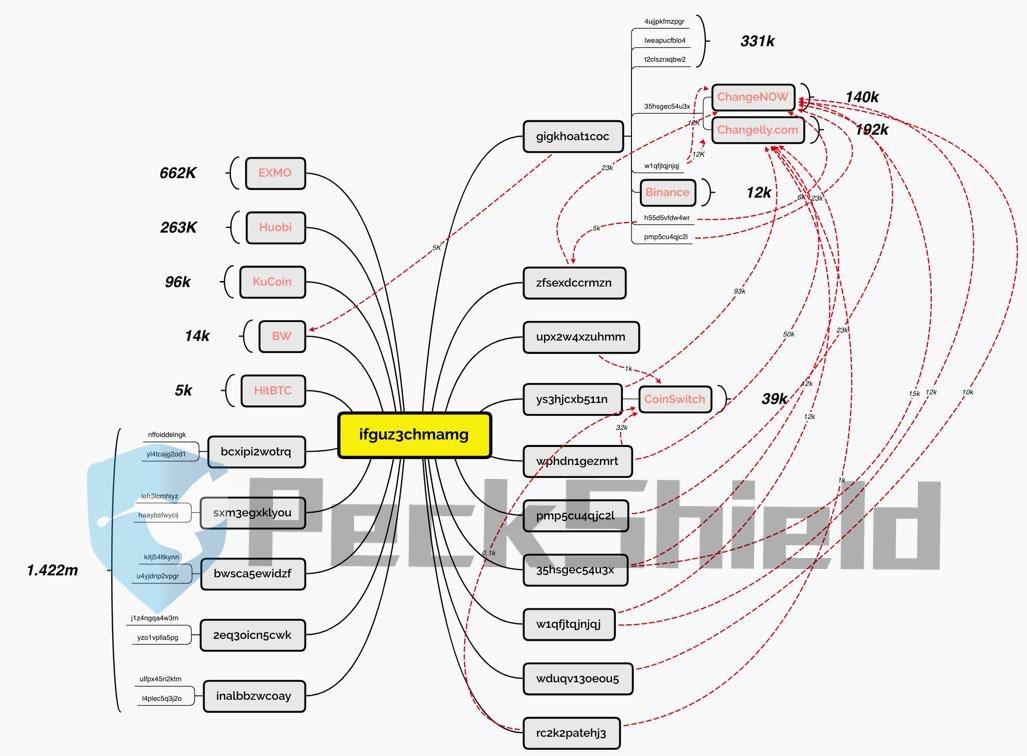
By this point Bithumb had started to move all the remaining funds from the hot wallet into the cold wallet. The stolen coins meanwhile were being laundered through an intricate web of back-and-forth transactions between multiple exchanges and addresses, as seen below.
The EOS attacker’s address can be found here (note the number of inbound transactions from people begging for money). By a few hours after the attack, the stolen coins had been tracked as far as the following exchanges.
Bithumb apologizes, suggests an ‘accident involving insiders’
The official Bithumb Twitter account sparked into action this morning to remind users that they’re funds were safe.
“We deeply apologize to our members for delaying the cryptocurrency deposit and withdrawal service, we would like to inform you of the circumstances of the grounds and confirm that your assets are safe.”
In the accompanying blog, the exchange operator appeared to confirm that the theft had involved people working at Bithumb. From the post :
“As a result of the internal inspection, it is judged that the incident is an ‘accident involving insiders’. Based on the facts, we are conducting intensive investigations with KISA, Cyber Police Agency and security companies.”
Bithumb says it ‘expects to recover’ the stolen funds, and that from now on it would be applying the same rigour to its internal security as it had its external:
“We constantly monitor and block external hacking. However, it was our fault that we only focused on defense of outside attack and lack of verification of internal staff.”