How Crypto Investor Stupidity Helped One Hacker Swipe $7 Million

Tron's super-duper amazing "next-generation" blockchain had an alarming flaw that would have allowed a single malicious PC to cripple the cryptocurrency. | Source: Shutterstock
By CCN.com: Years ago, a thief had a simple idea: figure out a way to guess Ethereum private keys and write software to sweep the crypto funds from the blockchain. Guessing the 72-character private key is no small feat – your odds are about 1 in 115 quattuorvigintillion . No, we didn’t make that number up.
The researchers told Wired that trying to do this without the help of high-powered computers would be like:
“[…] Choosing a grain of sand on a beach, and later asking a friend to find that same grain among a ‘billion gazillion’ beaches.”
The Fatal Flaw of Crypto ‘Brain Wallets’
The idea has blossomed into an incredibly successful business model, which capitalizes on malformed private keys and poor wallet development.
Wired reports on security researchers who uncovered this phenomenon and even proved the concept by sending funds to one of the wallets they suspected had been swept – within minutes the Ether disappeared to the address they believed was home to all the stolen cryptocurrency.
Most standard implementations of Ethereum wallets are immune to this problem. If a private key is generated correctly, it’s far less susceptible to guessing than if it is truncated by a character or two or worse, manually chosen by a person. A private key of all 0s or that sums up as 1 is the type of private keys that this sneaky fox is snatching.
In case our reader is new to blockchain technology, let’s briefly explain the nature of a private key. In private/public key cryptography, which all cryptocurrency is based on, ownership of the private key gives you access to anything associated with the public key – funds received or controlled by a Bitcoin or Ethereum address, for example. Bitcoin wallets are composed of multiple private keys, each corresponding to a public address, while the Ethereum system uses a single “account” architecture. A single private key in Ethereum will control all of that account’s Ether as well as its tokens. If someone compromises the private key, they can import the funds and then sweep them to somewhere else.
Tracking the Stolen Ethereum Funds
Wired doesn’t report which address keeps swiping, but says it has gained 45,000 Ether over the years. At the present time, that puts them in the top 400 Ether holders, which Etherscan tracks. So we had a look, and only a few addresses in the range of 44-46,000 have had a ton of transactions.
We think this one – 0x957cd4ff9b3894fc78b5134a8dc72b032ffbc464 – is the most likely account being referenced. Currently, it contains over $7 million in Ether and over $50,000 in other tokens. It’s had over 5,000 transactions, and a great many of these have been incredibly small. The script is indiscriminate – if any amount of Ether is moved into an address it has compromised, it swipes it immediately. As you can see if you visit Etherscan, it’s received dozens of nearly worthless transactions, the sum of which begins to add up.
As the Wired article points out, it’s no easy task to start guessing the identity of the criminal. However, it’s interesting to note that they seem to be hoarding Ethereum. There are less than 100 outgoing transactions, most of which happened a couple of years ago. It seems when the EOS token left Ethereum and became a reality, they redeemed the EOS the account held. It would be interesting to check the status of this account the next time the Ethereum price pushes toward $1,000.
All of which assumes this is the account that the Wired article speaks of, but it makes for a pretty good candidate. Here are the alternative options:
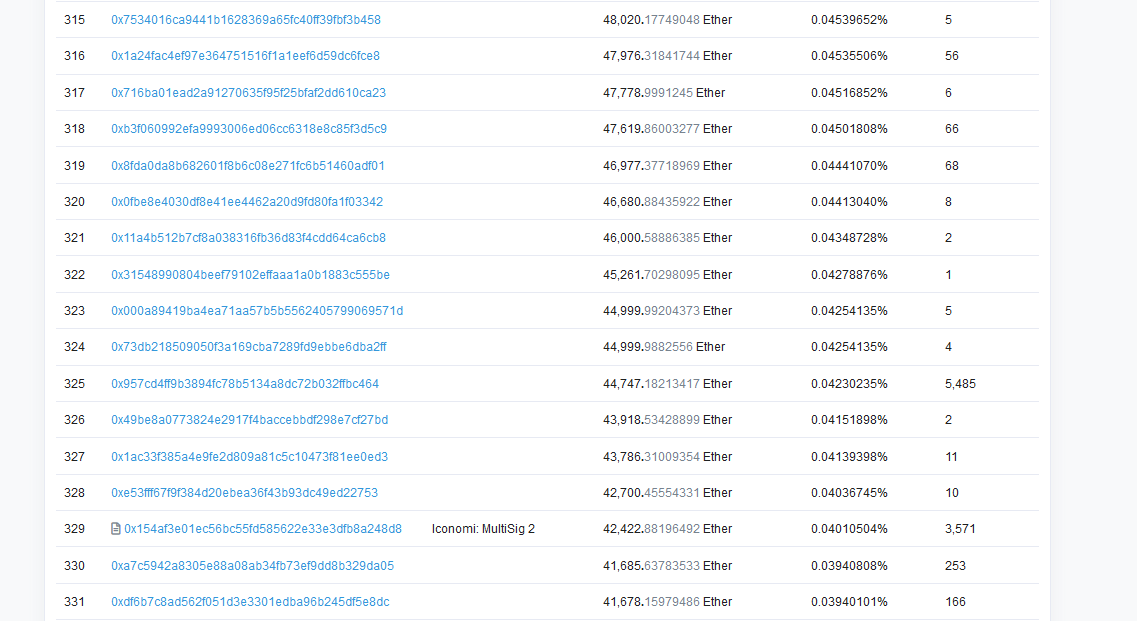
As you can see, most of the accounts in this range have far fewer transactions. The only other one with “thousands” of transactions belongs to an exchange.
Who did this, and hasn’t cashed anything out in years? Was it a rogue developer who wanted to discourage use of bad private keys, or highlight the insecurity of certain Ethereum wallets? Is it a state actor, as Wired suggests? It’s anyone’s guess at this point.