Billionaire Binance CEO Apologizes for Bitcoin Blockchain ‘Reorg’, a Dirty Word
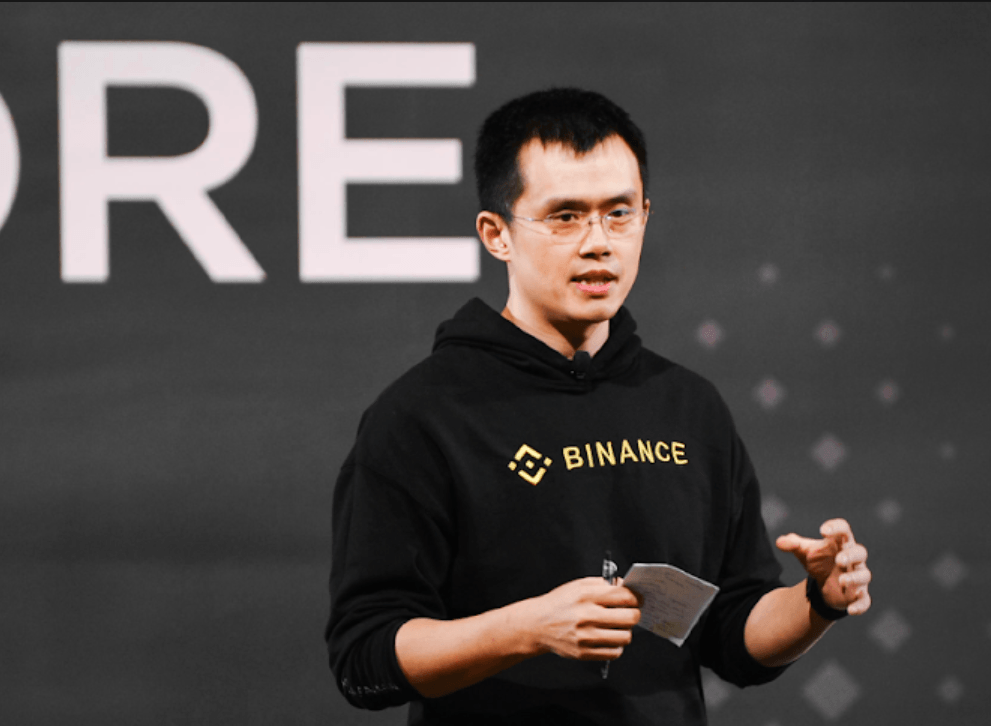
. | Source: Facebook/Binance
By CCN.com: Binance has posted an update about the security breach which cost the exchange around $40 million worth of bitcoins.
Binance CEO Throws Dirty Words Like “Reorg”
The message is a personal message from CEO Changpeng Zhao, who makes a few confessions during the post.
For one thing, CZ is no coder. He’s an executive. He probably spends too much time on Twitter. He took responsibility for starting a major discussion around the fundamentals of Bitcoin. On the advice of a couple of Bitcoin developers, his team had considered the notion of forcefully removing the funds from the hacker wallets.
“We will maintain constant communication with our community. I (CZ) am active on Twitter. In fact, some people even say I tweet too much. But my role is a facilitator and communicator. Honestly, I am not writing code or debugging servers. Given how much I talk, I sometimes say the wrong stuff, dirty words like “reorg”, for which I apologize. It is my strong view that our constant and transparent communication is what sets us apart from the “old way of doing things”, even and especially in tough times.”
Skip The Reorg — Attack The Fungibility of the Coins (?)
While this is an intriguing takeaway, perhaps the most important part of this missive is the implication that Binance and other exchanges are working together to, essentially, blacklist the stolen Bitcoins from “many exchanges and other service providers.”
“Many security and blockchain analytics firms are actively helping us track the stolen funds. We are also working closely with many exchanges and other service providers to freeze the stolen funds. It already is sort of an alliance. We have some ideas to contribute more on this front after we get over this incident.”
Unfortunately for Zhao, this is an industry version of denigrating the fungibility of Bitcoin.
While not as extreme as “reorganizing” the Bitcoin blockchain to take the proceeds of crime away from the criminals, it is another issue about which Bitcoiners feels strongly. A quick study of blockchain records by an educated researcher would reveal that a sizable percentage of the coins in circulation were once used in some crime or another. The reality is that all money is this way.
“Freezing” coins based on their provenance is a dangerous precedent, which essentially means that some bitcoins are good while others are bad. But if you work in a gas station and your customer hands you a $20 bill he just received from a drug transaction, it’s not your responsibility to know that. Similarly, it’s not the responsibility of any other exchange to investigate whether or not coins are from the Binance hack.
Privacy Coins May Be Our Only Hope
Is complete fungibility possible when one doesn’t need permission to know most of the details of a transaction? The concept has lead to a massive increase in the use of privacy-enhanced wallets such as Wasabi and a technology called CoinJoin. It is the fundamental value proposition for alternatives like Monero.
There is something that can be done besides “freezing” the coins. Existing laws require exchanges or money service providers of any sort (including payment processors) to report suspicious activity. Binance would stand a much greater chance of recovering part or all of its funds if it allowed these laws to work.
Ultimately, the coins have enduring value precisely because they can be spent and because they can be stolen – because they are the target of theft at all.
Every Exchange Eventually Fails, Binance Included
It’s not surprising to hear talk of “rolling back” the chain to “save our institution” when so many people came in around the same time as Binance itself. The influx of traditional finance means an influx of conventional ideas.
Radical or not, there are certain absolutes in crypto. Among them: immutability, fungibility, and ownership.
The blockchain is forever. Those coins will outlast Binance.
“Freezing” the coins might put them on hold for decades, but probably won’t put them back in Binance’s coffers. The proceeds of the Bitfinex hack were equally trackable. Some of them started moving not so long ago.
The rest of the post focuses on the various security measures Binance will take to ensure this type of breach never happens again. Binance users may note that the exchange intends to give away as many as 1000 YubiKeys . Perhaps they should give one to every user with balances over a certain level.
Disclaimer: the views expressed in this article belong solely to the author and should not be attributed to CCN.com.